The unprecedented digitization in our society has led many business leaders and managers to understand how to adequately assess and mitigate cyber risks.
Cyber risk management is a comprehensive process that aims to improve an organization’s cyber resilience. In this regard, governments are defining cyber-resilience obligations, identifying critical infrastructure that requires mandatory protection, and helping investors better benchmark their companies’ cyber performance.
Successfully managing cyber resilience is essential as organizations and managers face fines and other serious consequences. The potential consequences mean that board members must understand cyber risks and the best ways to mitigate them.
This is easier said than done. 93 percent of companies rely on their best practices to mitigate cyber risks, while 57 percent expect to be the target of a cyber attack. Unfortunately, only half of these organizations have implemented appropriate cyber initiatives.
Promoting Cross-Sectoral Cyber Resilience
In 2021, the World Economic Forum and its partners, together with the National Association of Company Directors (NACD), the Internet Security Alliance (ISA), and PwC, published The Principles for Management: Governance of Cyber Risk Forum on Cyber Risk Principles, which are critical to increasing sustainability in various industries.
This guide (originally developed for corporate boards) is summarized in six principles:
- Understand that cybersecurity is a strategic business enabler.
- Understand the financial drivers and implications of cyber risk.
- Align cyber risk management with business needs.
- Ensure the organizational structure supports cyber security.
- Bring cybersecurity expertise to government agencies.
- Encourage system flexibility and collaboration.
The principle represents a significantly different approach to resilience compared to how organizations delegate cybersecurity to IT, misunderstand the strategic nature of cyber risk and hide security breaches.
Misunderstanding the strategic nature of cyber risks can have enormous consequences. For example, software company Kasaye experienced a ransomware attack in July 2021 that delayed its planned initial public offering (IPO) until further notice after the company failed to raise about $875 million. In addition, SolarWinds, which was hacked in 2019, had special advertising techniques to show the business successes of its high-profile customers, ultimately providing the adversary with a “shopping list.”
Understanding Through Simulation
As cyber risk is on the agenda for managers, MIT CAMS has developed a method to improve managers’ ability to anticipate and manage cyber risk. Called the Cyber Risk Dashboard, the technology is based on management theory and system dynamics and is the result of significant industry research, including interviews with Chief Information Security Officers (CISOs). This has been confirmed over the years at Fortune 500 companies by analyzing many strategic cyber risk challenges.
Dashboard closely resembles the ecosystem of cyber risk decision-making. It examines the current defense posture and evolving attack tactics, emerging cyber events, and changing organizations in terms of people, processes, and technology. The Cyber Risk Dashboard provides the tools to make predictions against the performance indicators of an organization’s cybersecurity strategy. This work is easily applicable to other strategic analyses. MIT Cameras used a simulation-enhanced approach to understand organizational behavior by adapting the principles of the cyber risk forum.
Using personas—artificial decision-making profiles with specific characteristics that guide their cyber risk management strategy—is a scientifically sound approach to studying the behavioral side of cyber risk management. By using individuals from different organizations to make strategic decisions, this simulation technique can predict the future effects of their strategy.
In this analysis, we also reuse data from our anonymized case study of Fortune 500 company Smart Wealth Management Inc. As such, we identify:
CEO with a Cyber Consciousness (CC-CEO)
This CEO may be aware of the principles but has not yet embraced them. This executive focuses on prudent adherence to security standards and controls security costs. Growing workloads and scarce security resources are forcing a more responsive approach to cyber risk.
Resilient CEO (WEF-CEO)
This CEO is cyber-aware but has gone beyond adopting the Forum’s CyberRisk Principles to promote resilience. He may have signed the Forum’s Cyber Resilience Pledge. This CEO has a proactive and proactive approach to threats, knows how their technology drives their business, and is focused on maintaining business performance and anticipating the cost of cyber risks.
Strategic awareness increases cyber resilience.
We observe a significant difference when comparing the strength of the defense position, which indicates the number of security incidents and compromised assets. A CEO following the Forum’s Cyber Risk Principles (WEF CEO) is predicted to have up to 85 percent fewer cyber incidents (see Figure 1) compared to a CC CEO.
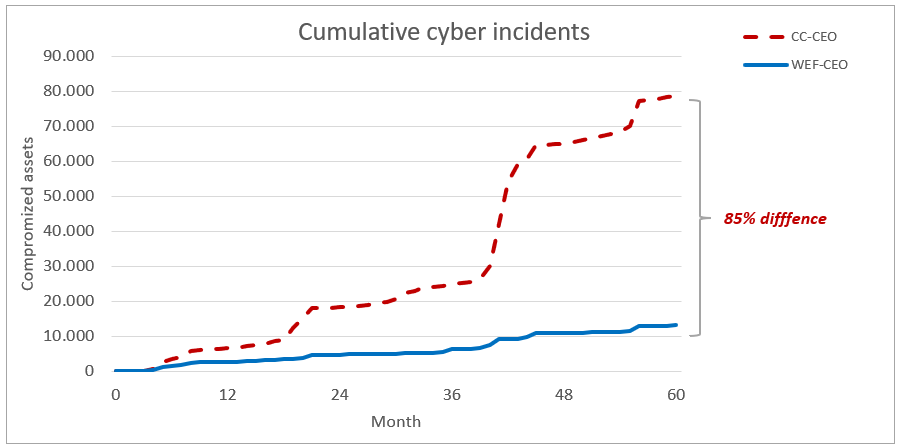
The WEF CEO’s cyber risk efforts and task prioritization allow for early intervention that limits adversary behavior, while the CC-CEO team often reacts more slowly, ultimately benefiting the adversary.
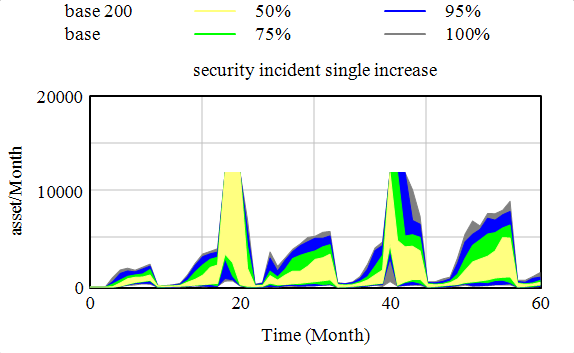
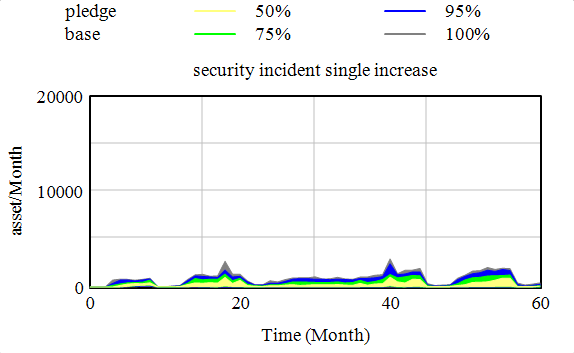
Similar views can be observed in the risk profile and Figures 2 and 3 in favor of the CEO of WEF regarding the frequency distribution of possible cyber incidents, mainly when a large number of cyber incidents may require IT, teams, to be assisted by security teams. Such situations, called handovers, require a change in the priorities of IT tasks, usually at the expense of the implementation of IT projects.
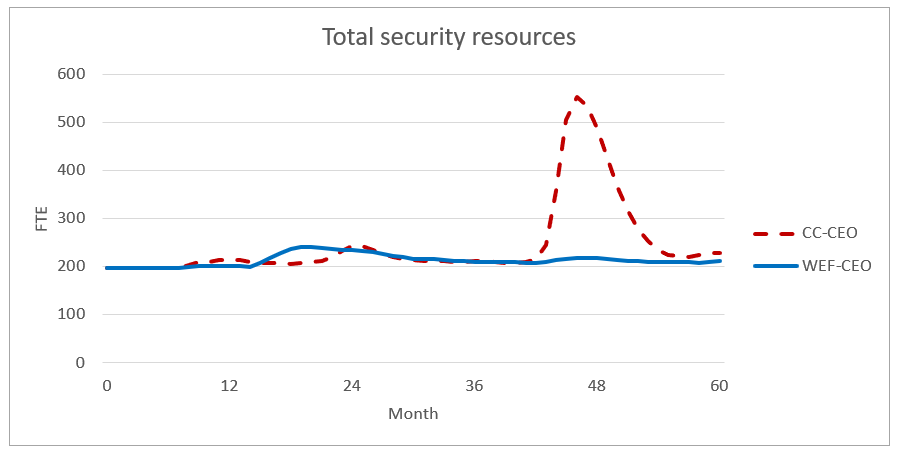
A sustainable approach does not increase costs.
WEF CEOs are likely to have lower costs than CC CEOs (see Figure 3). The main difference between these two scenarios is the priority of tasks and the cyber-risk efforts of security personnel. The CC CEO has a work in progress that will require additional staff resources to support response and recovery processes, conduct postmortems, and adapt and improve security capabilities accordingly. The WEF CEO’s implemented information security includes continuous proactive operational adaptation and improvement (including continuous automation) and regular executive-level cyber risk paneling and reporting.
Adopting the Forum’s Cyber Risk Principles demonstrates that individual organizations can significantly improve their cyber resilience at no cost. Adopting the principles proved valuable in those simulations. In practice, the interconnectedness and connectivity between organizations will lead to new interdependencies, which will be clarified through further research and simulations. However, the current findings themselves provide a strong case for organizations to adopt the forum’s cyber risk principles.
The MIT project was funded in part by the Fondo Europeo di Sviluppo Regionale Puglia.201 POR Puglia
2020, Asse I, Obiettivo specific 1a, Action 1.1 (RS), Titolo Progetto: Suite of Cybersecurity Products in Collaboration with BOC and SOC Cybersecurity at MIT Sloan (CAMS).
Source: WEF, MIT.





Leave a Reply